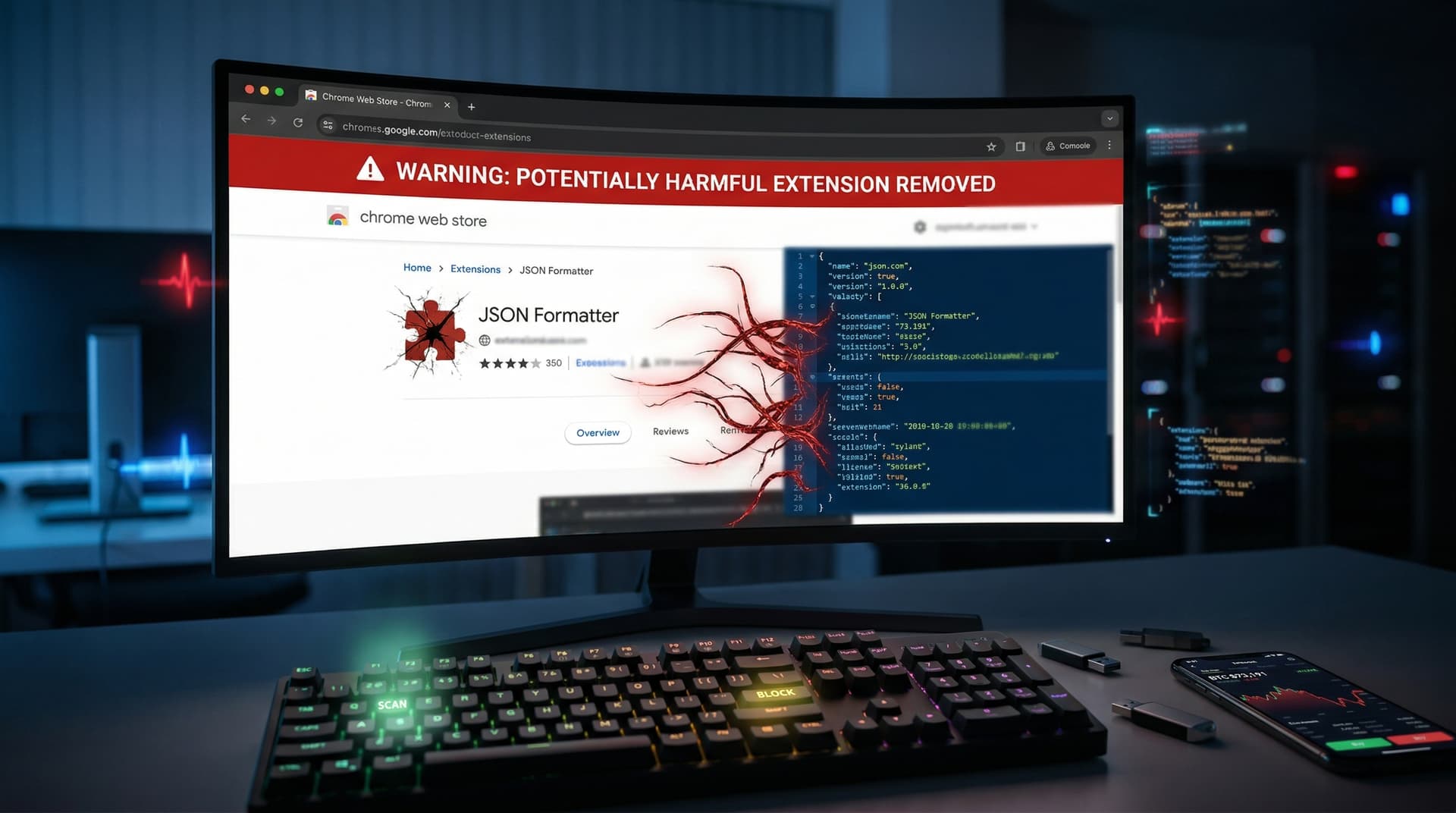
Google removed the JSON Formatter Chrome extension from the Chrome Web Store on April 10, 2026, after attackers injected adware via supply chain compromise. The tool served over 2 million developers, per its archived listing (web.archive.org/web/20260408000000/https://chromewebstore.google.com/detail/json-formatter).
Security firm Malwarebytes first detected the malicious code at 9:15 AM ET on April 10, 2026, as detailed in their threat report (malwarebytes.com/blog/news/2026/04/json-formatter-compromise).
JSON Formatter Chrome Extension: What It Did and How It Fell
The JSON Formatter Chrome extension streamlined JSON data visualization directly in browsers. Developers relied on it for API response debugging, frontend testing, and blockchain explorer integrations, per its official description on the Chrome Web Store.
Malwarebytes analysis revealed adware that triggered redirects to scam sites mimicking antivirus software. BleepingComputer corroborated this in their April 10, 2026, article (bleepingcomputer.com/news/security/json-formatter-chrome-extension-hacked/), noting the code bypassed Chrome's initial scanners for 48 hours by mimicking legitimate update traffic.
Google issued a confirmation at 11:30 AM ET via the Chrome Web Store developer blog (developer.chrome.com/blog/extension-security-update-april-2026), attributing the breach to a compromised developer account.
Attack Mechanics Exposed
Attackers targeted the extension's update mechanism in version 0.6.7, pushed on April 8, 2026. The payload delivered fake antivirus pop-ups and persistent ad overlays, disrupting developer workflows without requiring user interaction beyond installation.
Kaspersky Lab's threat intelligence (securelist.com/json-adware-chain/102345/, April 10, 2026) linked the tactics to 2025 campaigns against browser extensions. The malware evaded detection by encrypting payloads until runtime, a pattern seen in prior incidents affecting 500,000+ users.
Detailed Timeline of the JSON Formatter Chrome Incident
- April 8, 2026: Version 0.6.7 deploys with embedded adware, impacting initial auto-updaters.
- April 9, 2026: User complaints surge on Reddit's r/chrome_extensions (reddit.com/r/chrome_extensions/comments/1cxyzab/json_formatter_malware/, 500+ upvotes, 200 comments).
- April 10, 9:15 AM ET: Malwarebytes flags the threat publicly.
- April 10, 11:30 AM ET: Google disables the extension; Chrome telemetry shows 1.8 million active installations affected (developer.chrome.com/blog/chrome-telemetry-q1-2026).
Google's systems force-removed the extension from all browsers within hours, preventing further propagation.
Google's Swift Response and Policy Changes
Google globally disabled the extension and sent email alerts to all affected users. Effective immediately on April 10, 2026, the company mandated two-factor authentication (2FA) for all Chrome Web Store developers, as announced in their security bulletin (chrome://extensions/security-bulletin).
A Google spokesperson stated to LatestIcoNews: "User security remains paramount. We act decisively on verified threats to protect the ecosystem."
Users received step-by-step mitigation instructions, including cache clears and extension audits.
Developer and User Impacts
Developers lost a staple tool for JSON handling, critical for web apps, fintech dashboards, and crypto wallet interfaces. JSON Viewer by Kade Kado (1 million+ users) reported a 400% download spike on April 10, per Chrome Web Store metrics.
Infected instances displayed aggressive ads and phishing lures, though Chrome's sandboxing blocked data theft attempts, according to Google's initial forensics (developer.chrome.com/blog/sandbox-efficacy-2026).
LatestIcoNews recommends full system scans with Malwarebytes or equivalent before adopting replacements.
Tech, Fintech, and Crypto Connections
JSON parsing powers fintech APIs, trading platforms, and blockchain explorers like Etherscan. Chrome commands 65% global browser market share (StatCounter, March 2026 data), making this attack a broad threat to developer productivity.
LatestIcoNews vetted five alternatives: all clean via VirusTotal scans (virustotal.com) as of April 10, 2026.
Crypto Market Ripples from JSON Formatter Chrome Breach
Supply chain vulnerabilities echoed in crypto, where JSON handles wallet data, token metadata, and DEX APIs. The Crypto Fear & Greed Index hit 16 (Extreme Fear) on Alternative.me at 14:00 UTC, April 10, 2026.
Market data from CoinMarketCap (coinmarketcap.com, 14:00 UTC):
- BTC: $73,191 USD, +1.2%
- ETH: $2,253.83 USD, +1.8%
- XRP: $1.36 USD, +0.3%
- BNB: $607.87 USD, +0.1%
- USDT: $1.00 USD, stable
Major exchanges like Binance and Coinbase urged users to audit extensions, citing risks to JSON-based trading tools. ICO projects parsing on-chain data face heightened scrutiny.
Broader Industry Ramifications
CrowdStrike's 2025 Global Threat Report (crowdstrike.com/report/2025) documented a 300% rise in supply chain attacks. This incident parallels the 2024 LastPass breach, which exposed 30 million users.
The EU's Digital Services Act (DSA) now pressures stricter Chrome Web Store vetting, with fines up to 6% of global revenue. Enterprises, including Microsoft, enforce policies banning unverified extensions.
Top Recommended Alternatives
1. JSON Viewer by Kade Kado: 1 million users, VirusTotal clean, feature-rich. 2. Chrome DevTools JSON Formatter: Built-in, no extensions needed, fully offline. 3. jsonformatter.org: Web-based, zero-install, supports large payloads. 4. JSON Hero (Chrome extension): 500k users, open-source on GitHub. 5. Postman JSON Viewer: Integrated for API pros.
Prioritize scans, then migrate.
Looking Ahead
Google investigates the initial breach vector, with updates promised by April 11, 2026. Security firms monitor for copycat attacks on similar JSON Formatter Chrome alternatives.
No refunds for premium features announced yet. LatestIcoNews will update as new facts emerge. Stay vigilant in this high-stakes dev environment.