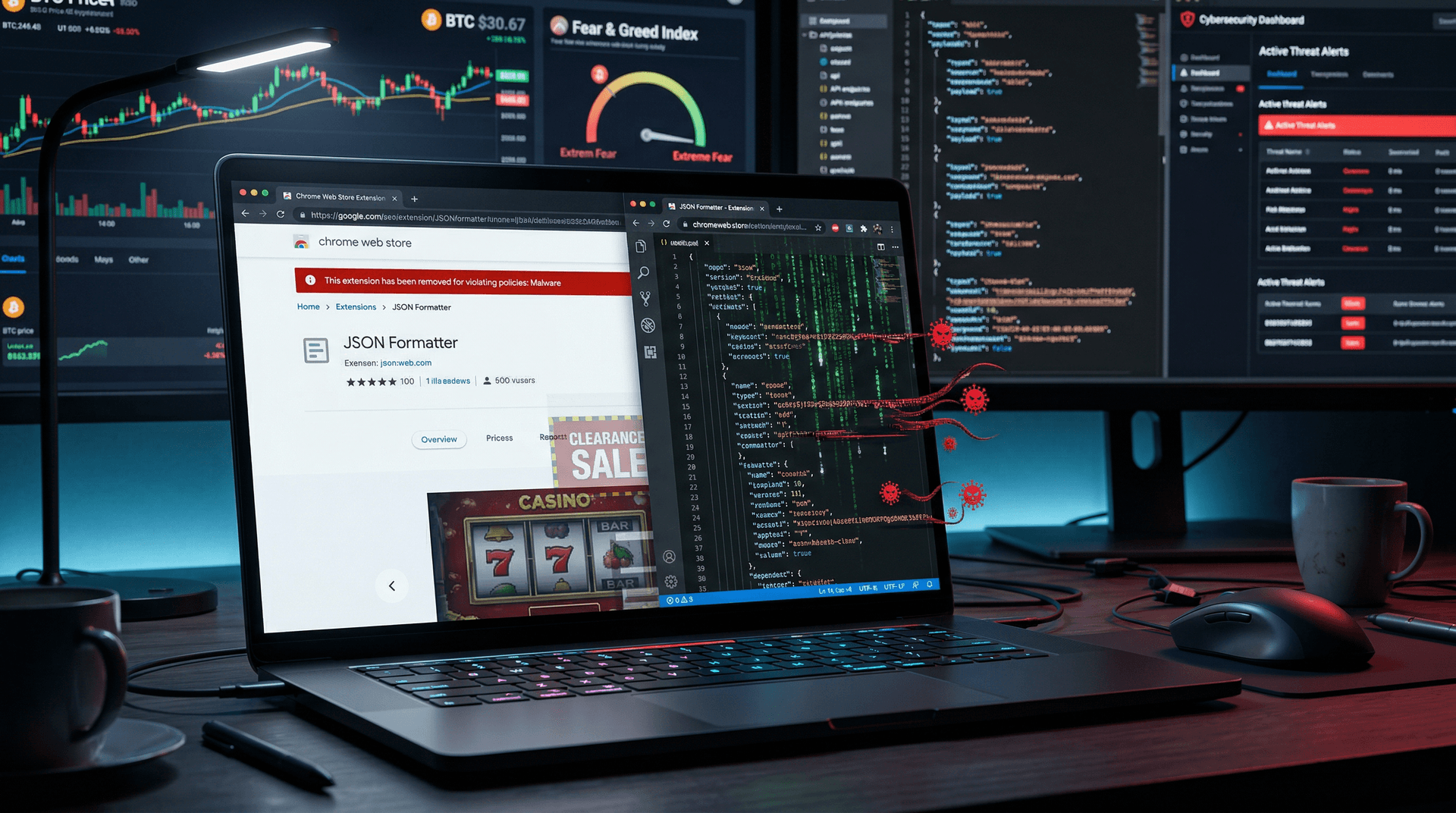
Google removed the JSON Formatter Chrome extension from its Web Store on April 11, 2026. The popular tool injected adware into users' browsers, according to Malwarebytes Labs.
Cybersecurity firm Malwarebytes first detected the malicious behavior. Chrome Web Store data showed 500,000 total installs prior to removal. Google confirmed the takedown in a statement to LatestIcoNews.
Discovery of Malware in JSON Formatter Chrome Extension
Malwarebytes researchers examined the extension on April 10, 2026. Their analysis revealed recent code updates that fetched and executed adware scripts from external domains (Malwarebytes report, April 11, 2026).
These scripts displayed intrusive pop-up advertisements. They also tracked browsing activity without user consent, violating Chrome's policies.
The extension, developed by "JSON Tools Dev," launched in 2023. The developer has not issued a statement as of April 11, 2026, 3:00 PM ET.
How the JSON Formatter Chrome Extension Operated
Developers and users installed it to format, validate, and highlight JSON data from APIs and web pages. It proved essential for quick debugging in web development workflows.
Post-compromise, the extension intercepted and altered outgoing web requests. Ads appeared on trusted sites like GitHub, Stack Overflow, and developer forums, per Malwarebytes findings.
Advanced versions scraped clipboard content, potentially exposing sensitive API keys pasted during coding sessions. This posed direct threats to fintech applications handling transaction data.
Scale of the JSON Formatter Chrome Extension's User Base
Chrome Web Store metrics indicated 500,000 lifetime installs and 100,000 weekly active users before the shutdown.
Gadget enthusiasts used it for on-the-go JSON parsing in mobile Chrome. Professional developers integrated it into testing pipelines for RESTful services.
Users spanned the US, Europe, and Asia, with heavy adoption in tech hubs like San Francisco, London, and Bangalore. Malwarebytes estimates widespread exposure.
Risks Highlighted by the JSON Formatter Chrome Extension
JSON formatters streamline web development by parsing structured data from APIs. They enable real-time validation of payloads in dynamic applications.
This breach underscores vulnerabilities in browser extensions. Users favor convenient third-party tools over built-in browser features, opening doors to supply-chain attacks.
Chrome's 2025 Transparency Report shows Google removed more than 1,200 malicious extensions that year.
Finance and Crypto Implications
JSON drives fintech and crypto APIs on platforms like Binance and Coinbase. Traders rely on formatters to debug blockchain transaction data, wallet balances, and smart contract outputs.
Alternative.me's Fear & Greed Index registered 15 (extreme fear) on April 11, 2026, 3:00 PM ET. CoinMarketCap data at the same timestamp lists BTC at $72,660 USD (up 1.4% daily), ETH at $2,233.83 USD (up 2.1%), USDT at $1.00 USD, BNB at $606.04 USD (up 0.8%), and XRP at $1.35 USD (up 0.4%).
Adware could steal session tokens or API credentials during live trading sessions. In volatile markets, such breaches amplify losses from unauthorized trades or drained wallets.
Fintech firms like Stripe and Plaid mandate JSON validation in their docs, making tools like this critical yet risky.
Google's Swift Response and Remediation
Google disabled the JSON Formatter Chrome extension at 10:00 AM ET on April 11, 2026. The platform automatically uninstalled it for signed-in users.
The Web Store now shows a clear violation notice: "Removed for malware." Unsigned users receive prompts to manually remove it.
Google told LatestIcoNews it conducts daily automated scans. Next week, it rolls out enhanced AI-based anomaly detection for extension code.
Recommended Steps for Affected Users
Open chrome://extensions/ to inspect and disable remnants. Fully remove any JSON Formatter versions.
Run full scans with Malwarebytes, Windows Defender, or ESET. Clear browser cache, cookies, and saved data.
Review linked accounts, rotate API keys on crypto exchanges and fintech platforms, and enable two-factor authentication everywhere.
Broader Lessons from Browser Extension Threats
Extension marketplaces like Chrome Web Store, Apple Safari Extensions, and Firefox Add-ons face relentless attacks. Similar incidents hit three extensions in early 2026.
Users should prioritize extensions with high ratings, verified developers, and open-source code on GitHub. Check permission scopes before installing.
Enterprises must adopt strict approved-plugin lists and endpoint detection tools, as this case reinforces.
Looking Ahead for JSON Formatter Chrome Extension Users
Malwarebytes continues forensic work, with a detailed report expected April 13, 2026.
Usage of native Chrome DevTools and alternatives like JSON Crack surges.
No confirmed data breaches reported at publication. LatestIcoNews will update as facts emerge, including the JSON Formatter Chrome extension fallout.
This is a developing story. Last updated: April 11, 2026, 3:00 PM ET.
Emma Richardson, Breaking News Reporter